Context
I have created and shared a Github project to help developers quickly deploy a Vuejs application using docker taking advantage of containerization capabilities offered by the Docker engine.
Once cloned, the project includes a folder app that has the minimal npm dependencies necessary for a Vuejs application. Thanks to GitHub code scanning enabled with Dependabot, it has identified high-priority, exploitable security issues in your code.
GitHub security advisory
When a security vulnerability is discovered in your project’s source code, GitHub sends an immediate notification to your email address with a comprehensive overview.
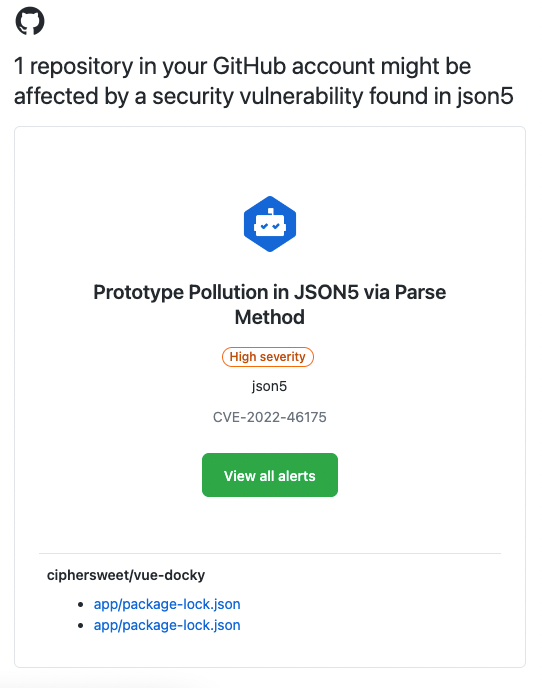
Identification of vulnerable packages
All alerts were raised because of vulnerable npm development dependencies:

Fixing the vulnerabilities
Cloning the project locally
git clone https://github.com/ciphersweet/vue-docky.git
cd vue-docky/app/
Even though GitHub scans our source code, it is wiser not to be fooled by appearances. There is an npm command that looks for vulnerabilities in used npm packages that are currently being used.
Let’s find out by running this command:
npm audit

While revising the audit report, I identified 64 vulnerabilities comming from dependencies. The key here is getting to the root package and fixing it.
Vulnerable packages
"dependencies": {
"core-js": "^3.6.5",
"vue": "^3.0.0"
},
"devDependencies": {
"@vue/cli-plugin-babel": "~4.5.0",
"@vue/cli-plugin-eslint": "~4.5.0",
"@vue/cli-service": "~4.5.0",
Fixed by updating them
"dependencies": {
"core-js": "^3.27.1",
"vue": "^3.2.45"
},
"devDependencies": {
"@vue/cli-plugin-babel": "^5.0.8",
"@vue/cli-plugin-eslint": "^5.0.8",
"@vue/cli-service": "^5.0.8",
Let's find out
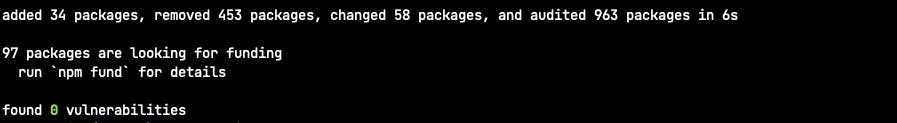
Conclusion
To maintain the security of a project, it is essential to continuously review and update the source code, using safe coding practices and keeping up to date with the latest security standards and vulnerabilities.
